Strengthen your business resilience to keep your organization prepared for disruptions today and in the future.
Ensure continued maturity of your BCM program
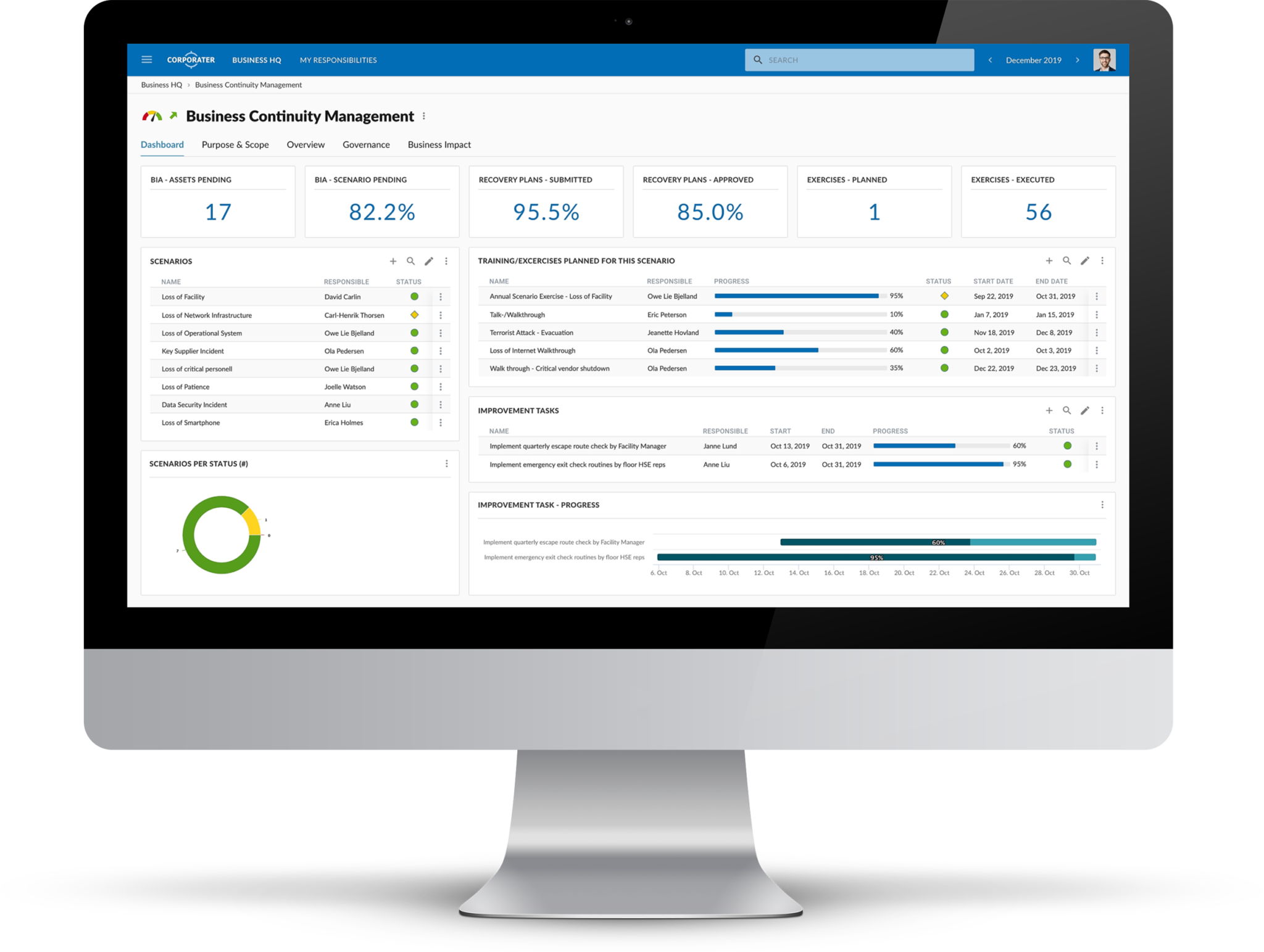
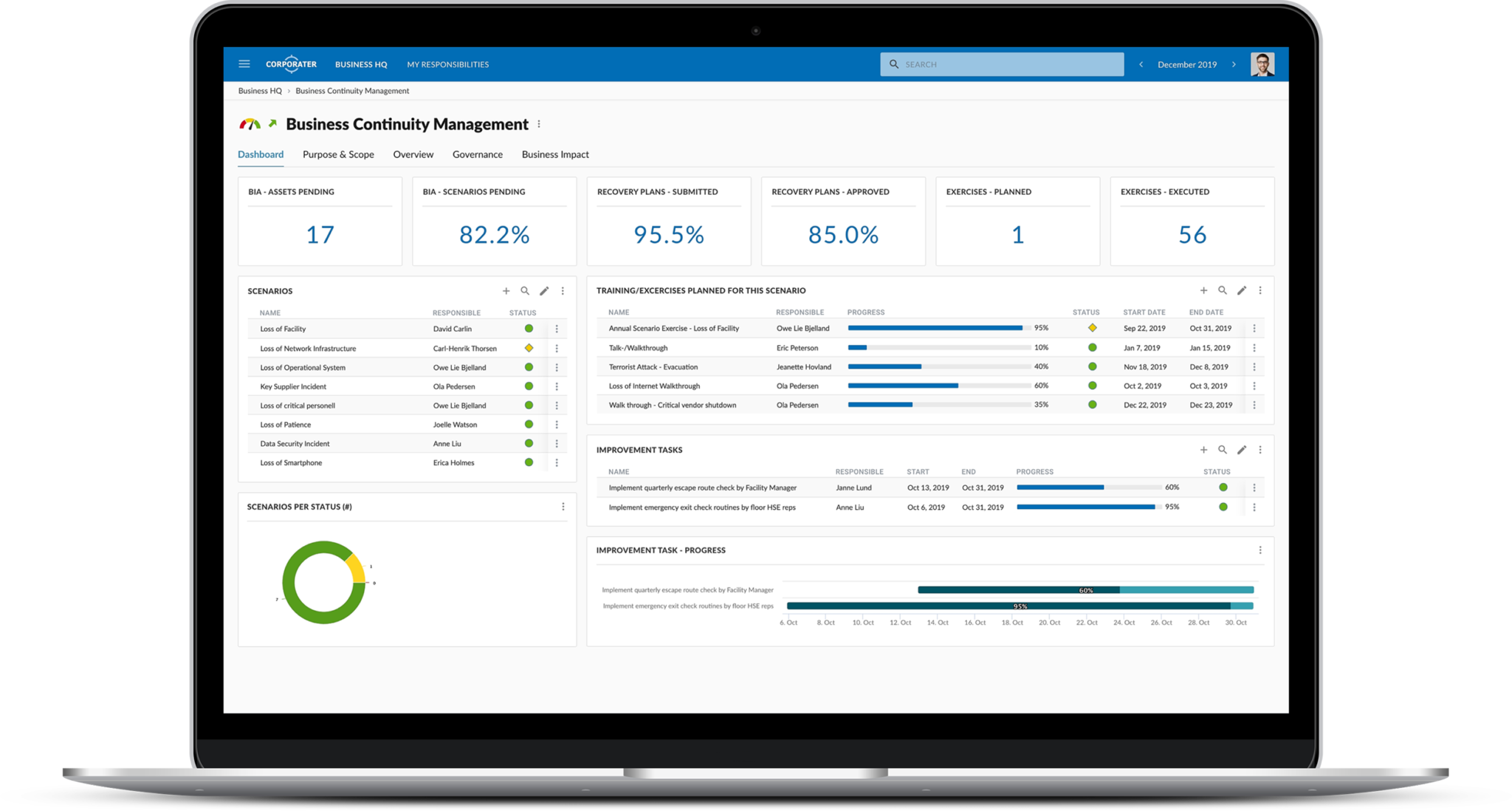
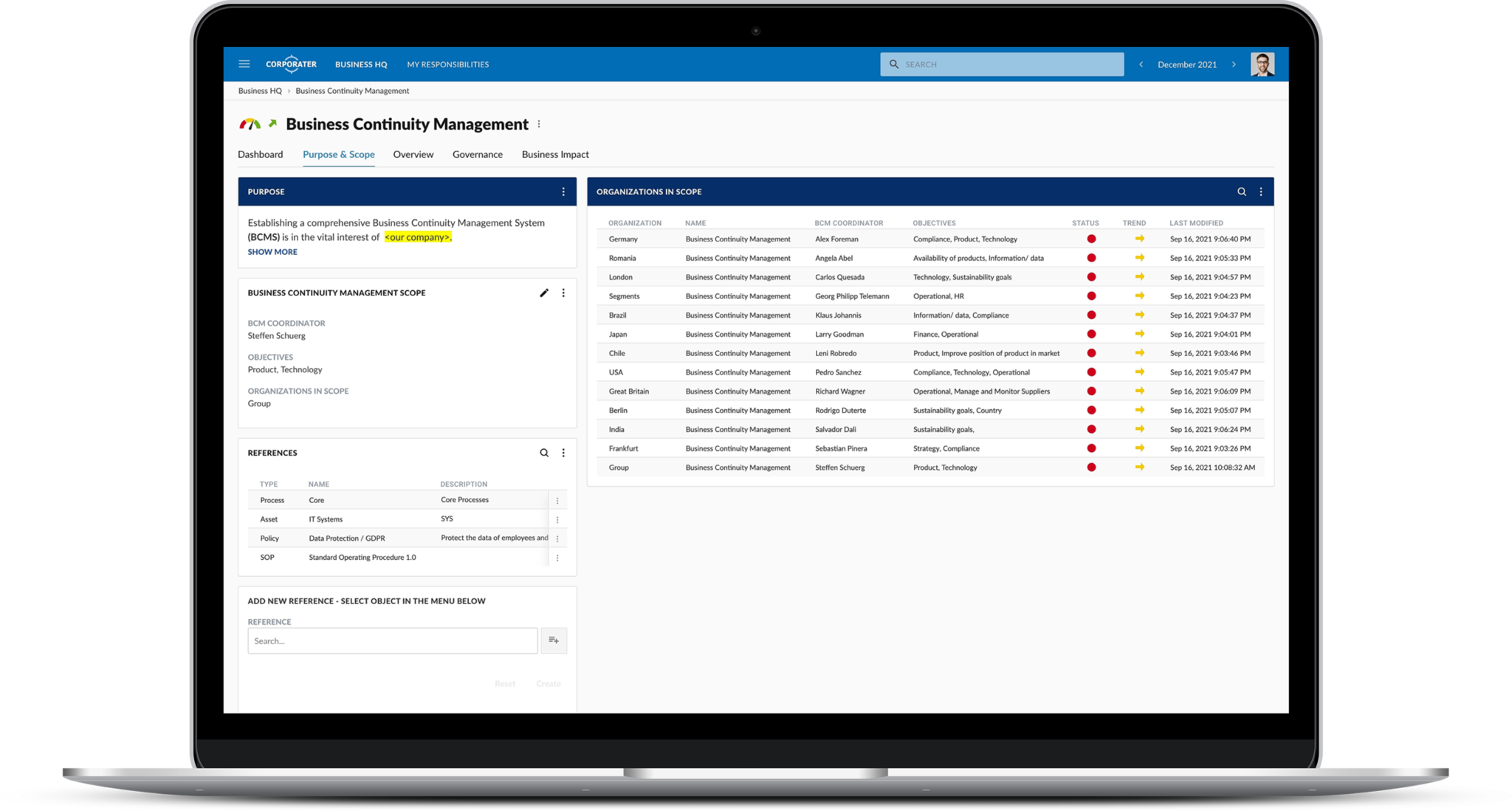
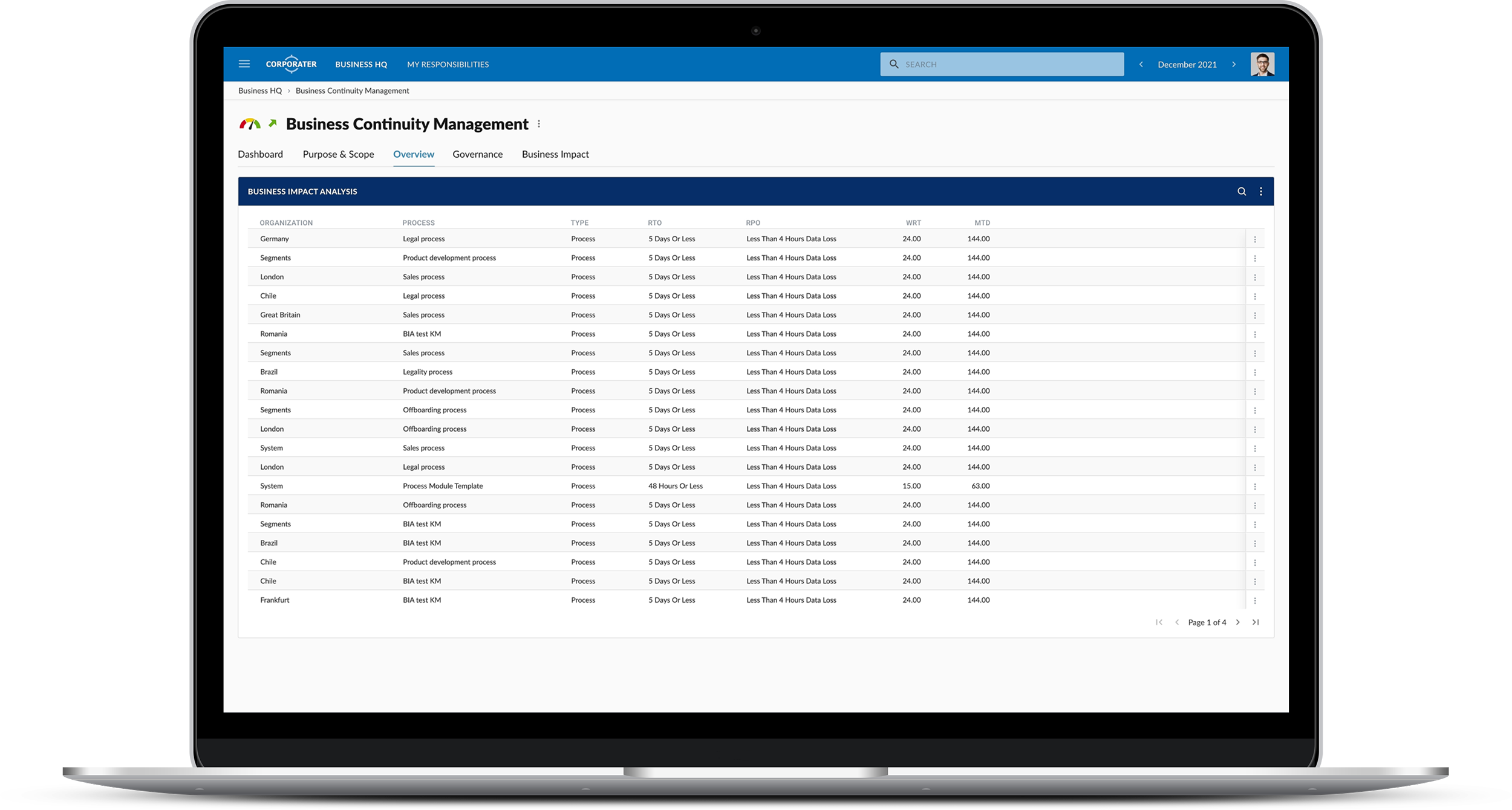
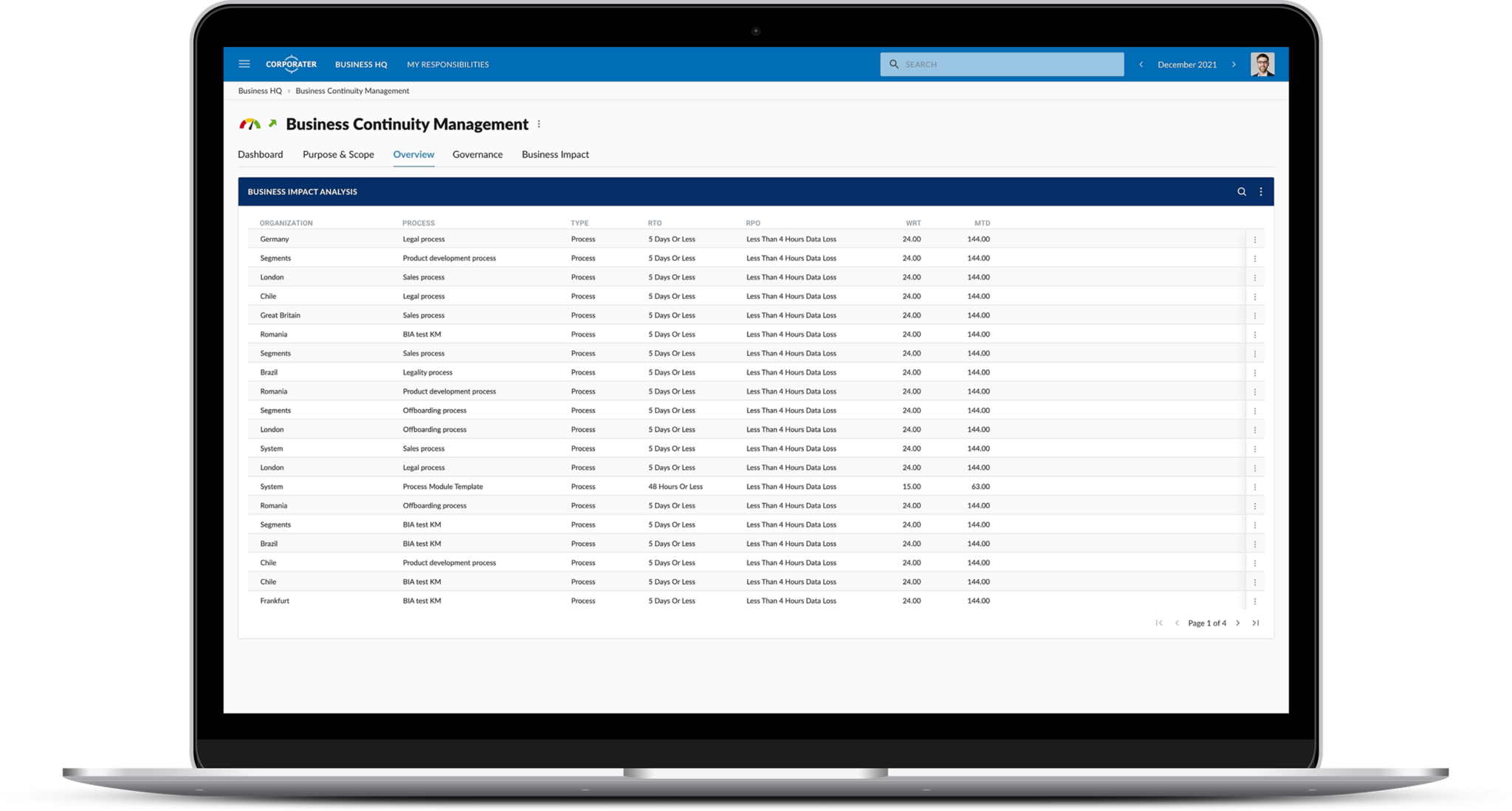
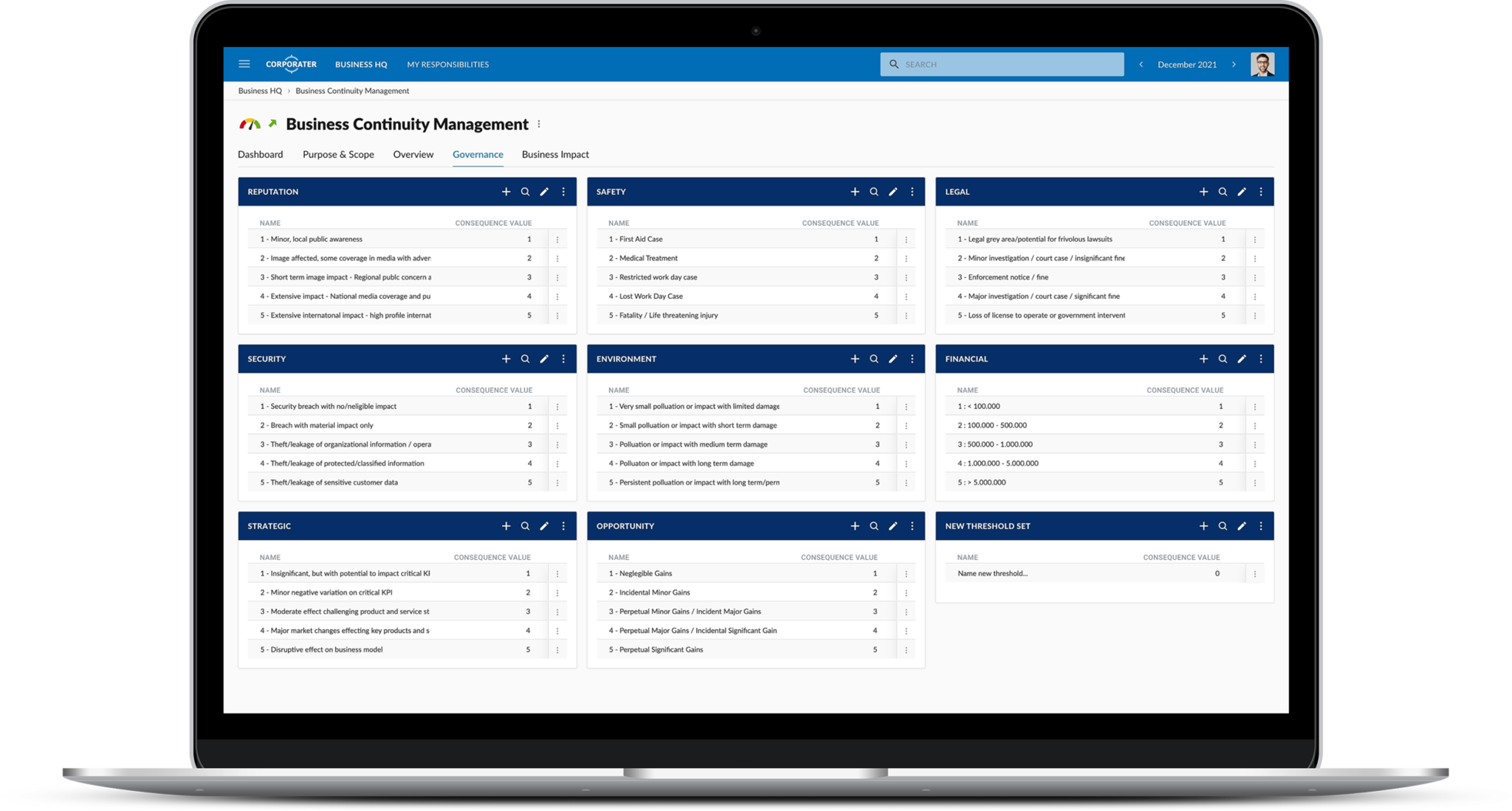
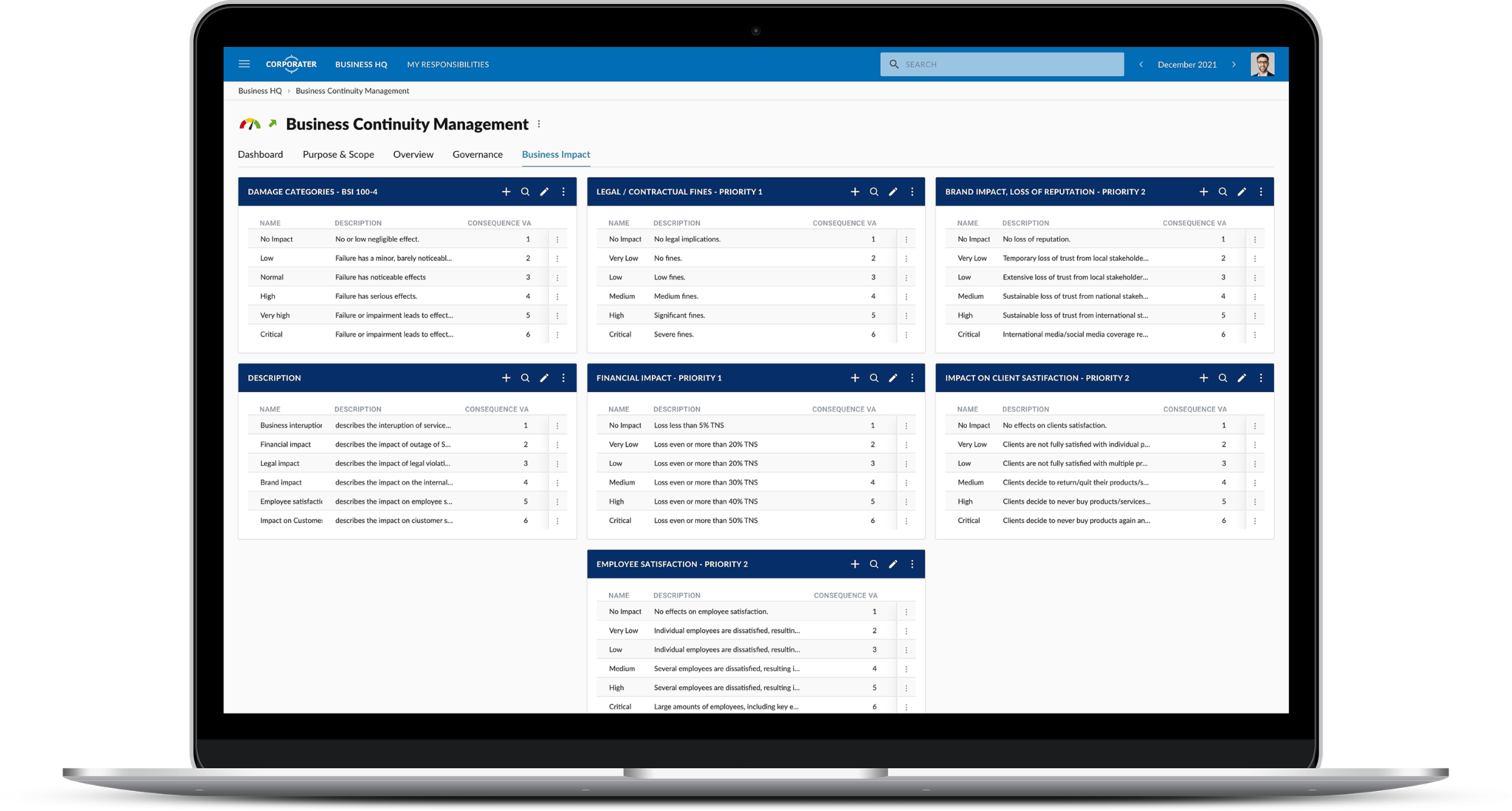
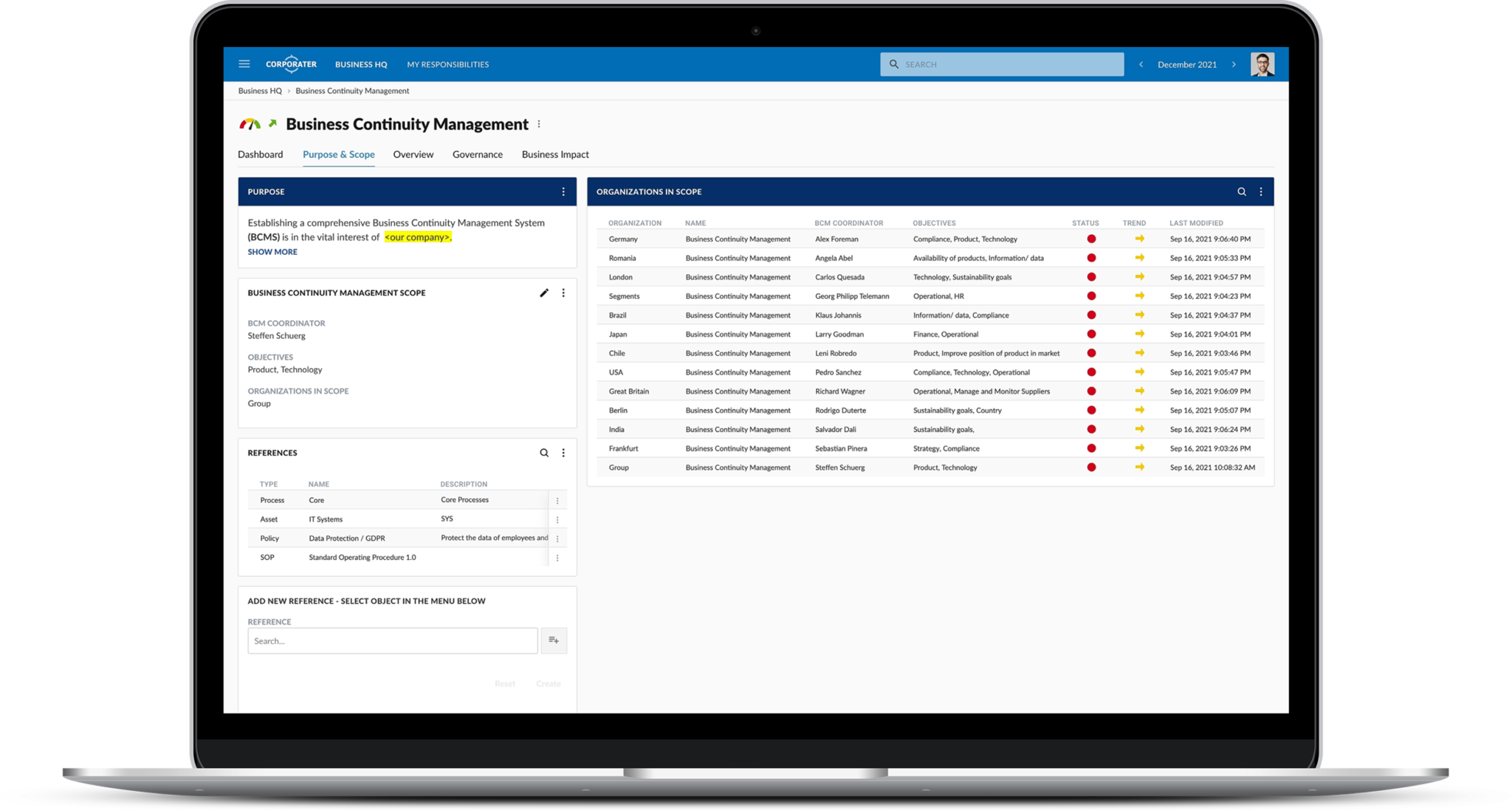
Ensure business continuity, regulatory compliance, and continued maturity of your BCM program with Corporater Business Continuity Management software. Identify your organization’s mission critical processes and assets, continuously monitor risks and threats, and develop detailed business continuity and disaster recovery plans to keep your organization prepared for internal and external disruptions.
Ensure business continuity, regulatory compliance, and continued maturity of your BCM program with Corporater Business Continuity Management software. Identify your organization’s mission critical processes and assets, continuously monitor risks and threats, and develop detailed business continuity and disaster recovery plans to keep your organization prepared for internal and external disruptions.